This talk is Jointly Sponsored by the
Department of Electrical and
Computer Engineering and the Department of Computer Science.
In-Depth Crypto Attacks
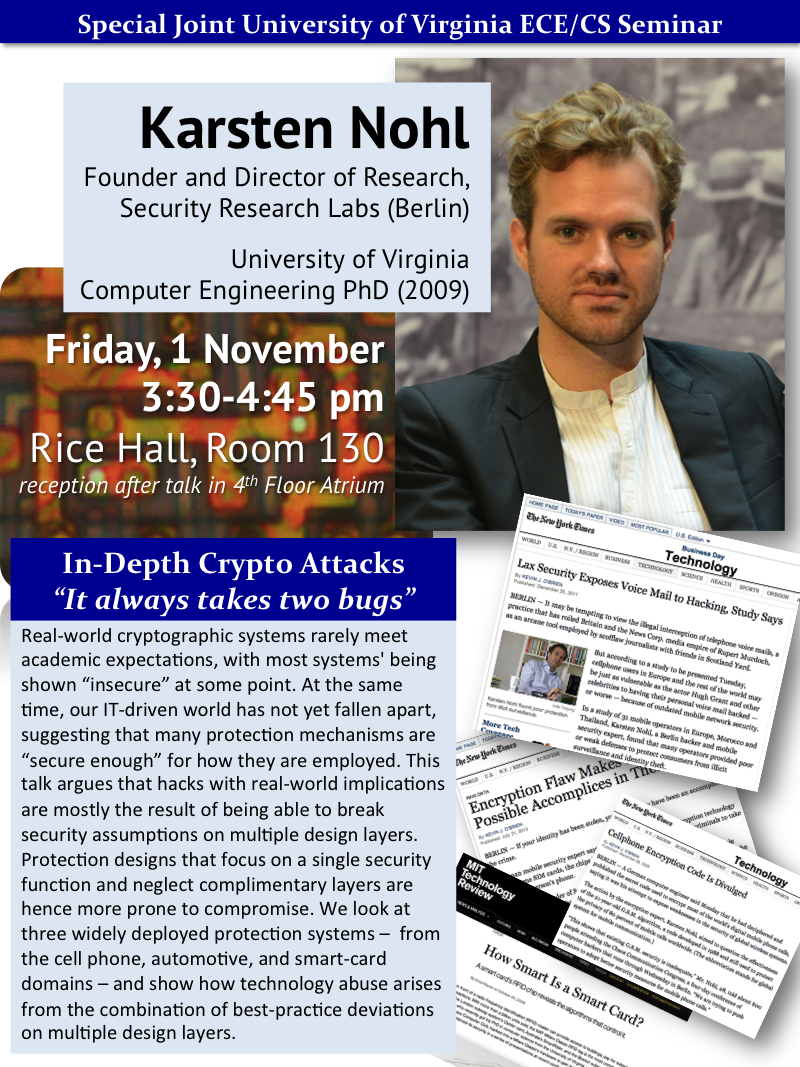
Karsten Nohl
Founder and Director of Research,
Security Research Labs (Berlin)
University of Virginia Computer Engineering PhD (2009)
 Real-world cryptographic systems rarely meet academic expectations, with
most systems' being shown "insecure" at some point. At the same time,
our IT-driven world has not yet fallen apart, suggesting that many
protection mechanisms are "secure enough" for how they are
employed. This talk argues that hacks with real-world implications are
mostly the result of being able to break security assumptions on
multiple design layers. Protection designs that focus on a single
security function and neglect complimentary layers are hence more prone
to compromise. We look at three widely deployed protection systems —
from the cell phone, automotive, and smart-card domains — and show how
technology abuse arises from the combination of best-practice deviations
on multiple design layers.
Real-world cryptographic systems rarely meet academic expectations, with
most systems' being shown "insecure" at some point. At the same time,
our IT-driven world has not yet fallen apart, suggesting that many
protection mechanisms are "secure enough" for how they are
employed. This talk argues that hacks with real-world implications are
mostly the result of being able to break security assumptions on
multiple design layers. Protection designs that focus on a single
security function and neglect complimentary layers are hence more prone
to compromise. We look at three widely deployed protection systems —
from the cell phone, automotive, and smart-card domains — and show how
technology abuse arises from the combination of best-practice deviations
on multiple design layers.
UVa Today News Article:
Renowned
'White Hat Hacker' to Speak on Real-World Security Holes,
Brevy Cannon, 29 October 2013.
University of Virginia graduate Karsten Nohl, one of the world's most
famous "white hat computer hackers," will speak Friday at 3:30 p.m. in
Rice Hall, room 130, about lessons learned from the security holes that
he and fellow researchers have uncovered in mobile phones, wireless car
keys and other technology used by billions of people everyday.

Nohl first made international headlines in 2008, while still a computer
engineering doctoral student at U.Va., for research that exposed
vulnerabilities in the world's most popular smartcard, used by millions
of people to pay fares on several major mass-transit systems around the
world, including the London Underground and the Boston subway.
...
Since graduating from U.Va. in August 2008, Nohl has gone on to discover
and demonstrate two key security vulnerabilities in mobile phones -
encryption flaws in both the GSM protocol that most cell phones use to
communicate with cell towers, and in SIM cards, the tiny "subscriber
identity module" chip in every phone that identifies and authenticates
the phone.
Both discoveries generated worldwide media coverage.
 Real-world cryptographic systems rarely meet academic expectations, with
most systems' being shown "insecure" at some point. At the same time,
our IT-driven world has not yet fallen apart, suggesting that many
protection mechanisms are "secure enough" for how they are
employed. This talk argues that hacks with real-world implications are
mostly the result of being able to break security assumptions on
multiple design layers. Protection designs that focus on a single
security function and neglect complimentary layers are hence more prone
to compromise. We look at three widely deployed protection systems —
from the cell phone, automotive, and smart-card domains — and show how
technology abuse arises from the combination of best-practice deviations
on multiple design layers.
Real-world cryptographic systems rarely meet academic expectations, with
most systems' being shown "insecure" at some point. At the same time,
our IT-driven world has not yet fallen apart, suggesting that many
protection mechanisms are "secure enough" for how they are
employed. This talk argues that hacks with real-world implications are
mostly the result of being able to break security assumptions on
multiple design layers. Protection designs that focus on a single
security function and neglect complimentary layers are hence more prone
to compromise. We look at three widely deployed protection systems —
from the cell phone, automotive, and smart-card domains — and show how
technology abuse arises from the combination of best-practice deviations
on multiple design layers.
